Explore key tools, smart features, and expert insights...
In a hybrid work environment, verifying a user’s identity is just one part of securing access. Even when credentials are correct, an insecure device or an unmanaged session can expose sensitive corporate data.
Browser sessions are the new perimeter, and gaps between identity verification and session security are a common attack vector. Attackers often exploit this gap through session hijacking, stolen cookies, or compromised endpoints.
Chrome Enterprise Premium (CEP) uses Device-Bound Session Credentials (DBSC) to tie user sessions to specific, compliant devices. This ensures that even if login credentials are stolen, they cannot be reused on an unauthorized device.
By bridging identity and device security, CEP enforces a zero-trust model at the browser layer:
Validates both the user and the device before granting access.
Prevents active session theft from exposing critical applications.
Reduces the risk of unverified devices interacting with sensitive systems.
Before deploying policies, IT teams need clarity on where session and identity gaps exist. The CEP Accelerator, part of the Chrome Readiness Tool, provides actionable insight into these risks. It shows which devices are unprotected due to outdated browser versions. This approach moves security planning from guesswork to data-driven prioritization.
The combination of CEP enforcement and CEP Accelerator visibility ensures that identity security and browser sessions are no longer siloed, providing a cohesive defense against modern threats.
Identity verification alone cannot secure sessions.
Device-bound session enforcement ties sessions to trusted endpoints, creating a zero-trust browser layer.
CEP Accelerator provides visibility into gaps between identity and session security.
IT teams can take measured, prioritized action, closing exposure efficiently.
By linking identity, device trust, and session enforcement, organizations can eliminate hidden browser vulnerabilities, reduce exposure to session hijacking, and strengthen the overall security posture of their digital workplace.

Enterprise applications are accessed through the browser more than ever before. From finance systems to internal dashboards, users authenticate once and interact with multiple services throughout the day. While this improves productivity, it also increases the risk of credential theft across applications.
Attackers no longer rely only on stolen passwords. Instead, they target browser-stored data such as session tokens, saved credentials, and autofill information to gain access without triggering traditional security controls.
Credential exposure does not happen in isolation. It is often the result of multiple risk factors across the browser environment:
Outdated Browsers: Older versions may lack the latest protections, making session data easier to exploit
Unverified Extensions: Extensions from unknown or untrusted sources can access browser data and introduce vulnerabilities
Unsecured Domain Access: Visiting non-HTTPS or restricted sites increases the risk of data interception
Local Data Storage: Credentials and session tokens stored on the device can be extracted if not properly protected
These risks compound across applications, allowing attackers to move from one system to another once access is gained.
Chrome Enterprise Premium (CEP) provides controls to reduce credential theft risk at the browser level:
App-Bound Encryption: Ensures that only the browser can access stored credentials and session data
Policy Enforcement: Applies consistent security controls across all users and devices
Secure Access Controls: Limits how sensitive data is accessed and used within browser sessions
These protections help prevent attackers from extracting usable credentials, even if they gain access to the device.
Before applying controls, IT teams need to identify where credential risks exist across their environment. The Chrome Readiness Tool, through its Browser Insights feature, provides this visibility.
Browser Insights evaluates:
Browser and Extension Details: Tracks browser versions and installed extensions across all devices
Security Threats: Flags unverified or outdated extensions and highlights session theft vulnerability based on browser version
Access to Unsecured Domains: Identifies visits to non-HTTPS or restricted domains
Devices running the latest browser version are marked as protected, while outdated browsers are marked as not protected, indicating higher exposure to credential misuse.
The Browser Security Insights dashboard consolidates these findings and assigns a security status to each device. A device is marked Secure only if it has no unverified extensions and no restricted domain activity.
Administrators can drill down into device-level data to view installed extensions, browsing behavior, and session protection status. This enables IT teams to pinpoint which endpoints are most likely to expose credentials across applications.
The CEP Accelerator, within Browser Insights, helps translate these findings into actionable insight.
It connects observed risks to Chrome Enterprise Premium capabilities by showing:
Which devices with outdated browsers increase credential exposure across applications
How extension risks and unsecured browsing contribute to credential theft
This turns raw data into a clear plan, helping IT teams focus on the areas that matter most.
Credential theft is no longer limited to stolen passwords. Browser data such as session tokens and stored credentials creates new opportunities for attackers to access multiple applications.
With Chrome Enterprise Premium, organizations can protect credentials through app-bound encryption and policy enforcement. With Chrome Readiness Tool’s Browser Insights, they gain visibility into outdated browsers, risky extensions, and unsafe browsing behavior.
The CEP Accelerator bridges the gap between visibility and action, helping IT teams prioritize and apply the right protections.

In today’s enterprise environment, browsers are more than a portal to the web they are repositories of corporate data. Employees access sensitive applications, download documents, and interact with SaaS tools daily. Yet, a critical security gap persists: data at rest in browsers.
While many organizations focus on network and cloud protections, local data stored on devices is often ignored. This includes cached pages, session tokens, temporary downloads, and form entries. If left unprotected, this data can be extracted by malicious actors or misused if a device is lost or stolen.
Browser data is designed for speed and convenience, but those benefits come with risk:
Cached Credentials: Session tokens or login information stored locally can be copied and misused to access corporate accounts.
Temporary Files: Documents opened or downloaded for brief use may remain on the device after the session ends.
Form Data Exposure: Data entered in web forms, including personal and financial information, can be reconstructed if not encrypted.
These overlooked risks make endpoints a prime target, especially in hybrid or BYOD environments where devices may not be fully managed.
Chrome Enterprise Premium (CEP) addresses these vulnerabilities by enforcing strong protections for browser data at rest:
Disk Encryption for Browser Cache: All cached data is encrypted locally, preventing unauthorized access if the device is lost or stolen.
App-Bound Encryption: Only the browser itself can access cached data, stopping malware or other applications from extracting sensitive information.
Policy Enforcement Across Devices: CEP ensures both managed and BYOD endpoints comply with encryption policies, reducing risk across the organization.
By combining these protections, CEP mitigates the exposure of sensitive corporate data and supports regulatory compliance.
Before applying these protections, IT teams need a clear view of where sensitive data may be stored locally. The Chrome Readiness Tool, through its Browser Insights section, provides this visibility:
Browser and Extension Details: Reports the browser type, version, and installed extensions for every device, helping teams understand potential risk vectors.
Security Threats: Flags unverified or outdated extensions and identifies devices with Session Theft Vulnerability, which can expose cached session data.
Access to Unsecured Domains: Tracks visits to non-HTTPS sites or restricted domains, which may cause sensitive data to be stored locally.
Administrators can review this information in the Browser Security Insights dashboard. Devices are marked Secure only if they have zero unverified extensions and no visits to restricted domains. Drill-down capability allows IT teams to view device-level extension lists, accessed URLs, and session protection status.
This insight allows teams to identify endpoints that may store sensitive data insecurely, prioritize remediation, and enforce protective measures proactively.
Without visibility and encryption:
A lost or stolen device could expose cached payroll data, contracts, or session credentials.
Malware could extract sensitive browser data from unprotected caches.
IT teams lack a clear view of which endpoints are high-risk.
With CEP and Browser Insights:
Cached data is encrypted and accessible only by the browser.
Devices with unverified extensions or unsafe domain activity are clearly flagged.
IT teams can target remediation on devices that actually handle sensitive data locally.
Data at rest in browsers is an often-overlooked vulnerability that can compromise sensitive corporate information. By leveraging Chrome Enterprise Premium to enforce encryption and Chrome Readiness Tool’s Browser Insights to provide visibility, organizations can identify risky endpoints, secure cached data, and maintain control across hybrid and BYOD environments.

In modern enterprises, authentication alone isn’t enough. Even a verified user can introduce risk if their device is unmanaged, compromised, or misconfigured. Sensitive systems like HR portals, financial dashboards, and internal applications require device-bound session protections to prevent unauthorized access.
Chrome Enterprise Premium (CEP) enforces Device-Bound Session Credentials (DBSC), ensuring that sessions are tied to a compliant device. This means stolen session cookies or credentials are useless outside the original device, protecting your organization from session hijacking attacks.
Before applying DBSC policies, IT teams must understand where exposure exists. Without visibility, enforcement can be inconsistent:
Some devices may already have DBSC enabled.
Others might be unmanaged or missing key policy configurations.
Critical applications could remain exposed due to uneven policy coverage.
Applying policies blindly risks either operational disruption or residual security gaps.
The CEP Accelerator, a specialized layer within the Chrome Readiness Tool, transforms device and session data into actionable insight. It helps IT teams understand which devices are protected, which are not. It provides a high-level view of session protection coverage across your organization.
This visibility allows teams to prioritize enforcement based on risk, rather than applying blanket policies that may disrupt workflows.
With visibility in hand, IT teams can:
Identify unprotected devices accessing critical applications.
Apply device-bound session policies efficiently to those endpoints.
Monitor ongoing compliance and update policies as devices or usage patterns change.
Ensure that only secure, compliant devices can initiate sensitive sessions.
The CEP Accelerator ensures that your deployment strategy is data-driven, targeted, and measurable.
Visibility is a prerequisite for effective device-bound session enforcement.
CEP Accelerator converts raw device and session data into policy-aligned insights.
Prioritize enforcement for devices and sessions with the highest exposure.
Continuous monitoring ensures that your browser sessions remain secure across all endpoints.
By combining device-bound session enforcement with CEP Accelerator insights, organizations protect sensitive data, prevent session hijacking, and maintain operational efficiency across hybrid and BYOD environments.

Modern enterprises rely heavily on browsers to access applications, manage workflows, and handle sensitive data. From login credentials to session tokens and downloaded files, a significant amount of business-critical information flows through the browser daily.
This makes the browser a prime target for infostealer malware. Unlike traditional threats, infostealers are designed specifically to extract sensitive data from local environments, often without triggering immediate alerts.
Infostealer malware focuses on harvesting data stored within the browser and the underlying system. This includes:
Saved Credentials: Usernames and passwords stored in the browser
Session Tokens: Active session cookies that allow attackers to bypass login controls
Autofill Data: Personal and corporate information entered into forms
Downloaded Files: Sensitive documents temporarily stored on the device
Once extracted, this data can be used to access enterprise applications, impersonate users, or move laterally across systems.
Browsers are designed for usability, which means they store and manage data locally to improve performance. However, this creates multiple exposure points:
Data is accessible at the device level, especially on unmanaged or BYOD endpoints
Malicious applications can attempt to read browser storage if protections are not in place
Users may unknowingly install extensions or software that introduce risk
Even a single compromised device can expose multiple applications, making browser-level protection essential.
Chrome Enterprise Premium (CEP) introduces protections specifically designed to reduce the risk of credential theft and data extraction:
App-Bound Encryption: Restricts access to browser data so only the browser itself can read it, preventing external applications from extracting credentials or session data
Protection Against Infostealers: Blocks unauthorized access attempts to sensitive browser storage
Policy-Based Controls: Ensures consistent protection across managed, unmanaged, and contractor devices
These controls help limit the ability of malware to extract usable data, even if a device is compromised.
Before enforcing protections, IT teams need to understand where risks exist across their environment. The Chrome Readiness Tool, through its Browser Insights feature, provides visibility into potential exposure points.
Browser Insights helps identify:
Risky Extensions: Unverified or outdated extensions that may introduce vulnerabilities
Session Theft Vulnerability: Devices where session theft is possible, increasing exposure to credential misuse
Unsecured Domain Access: Visits to non-HTTPS or restricted domains that may expose sensitive data
This information is presented in the Browser Security Insights dashboard, where each device is evaluated based on these risk indicators. Devices are marked Secure only when no unverified extensions or risky domain activity is detected.
Administrators can drill down further to view device-level details, including installed extensions and browsing activity. This helps pinpoint where sensitive data may be exposed or at risk of extraction.
The CEP Accelerator, within Browser Insights, helps IT teams interpret these findings in the context of credential theft risk.
It provides clarity on:
Which devices are more likely to expose browser-stored credentials
How extension risk and browsing behavior contribute to potential data extraction
Which CEP protections, such as app-bound encryption, address these risks
Rather than just presenting raw data, it connects exposure points to the specific controls that reduce them.
Organizations can take a structured approach to mitigating infostealer risk:
Assess: Use Browser Insights to identify risky extensions, unsecured browsing, and session vulnerabilities
Analyze: Leverage CEP Accelerator to understand how these risks relate to credential exposure
Protect: Apply app-bound encryption and CEP policies to secure browser data
Monitor: Continuously track device posture and maintain protection coverage
This approach ensures that protections are applied where they are most needed, reducing both risk and operational disruption.
Infostealer malware targets one of the most valuable assets in the enterprise: browser data. Without proper controls, credentials, session tokens, and sensitive information can be extracted and misused.
With Chrome Enterprise Premium, organizations can prevent unauthorized access to browser data through app-bound encryption. With Chrome Readiness Tool’s Browser Insights, they gain visibility into where risks exist.
The addition of CEP Accelerator bridges the gap between insight and action, helping IT teams prioritize and apply protections effectively.
Start by identifying where your browser data is exposed, then use CEP to secure it before attackers do.
In modern enterprise environments, browsers are not just tools they’re critical workspaces where employees access and interact with sensitive information. From payroll records to confidential contracts, much of this data passes through browser sessions. While convenient, temporary browser storage like caches introduces a hidden risk: data exposure at rest.
Many organizations focus on server and cloud security, but cached browser data often remains overlooked. Cached files, session tokens, and downloaded documents can be reconstructed if a device is lost, stolen, or compromised. Without proper visibility and enforcement, this creates a significant compliance and security risk.
Browser caches store temporary data to improve performance, but they also store sensitive information that could be exploited:
Session Tokens: Cookies stored locally can be extracted and reused to access corporate accounts.
Form Data: Employee or customer data entered in forms may remain in cached files even after logging out.
Temporary Downloads: Documents stored for quick access can be retrieved by unauthorized users or malware.
Even a single lost or unmanaged device can put an organization at risk, highlighting the need for proactive data protection measures.
Chrome Enterprise Premium (CEP) provides strong protections for local data with two key features:
Browser Cache Encryption: Data stored in the cache is encrypted on disk, making it unreadable if a device is lost or stolen.
App-Bound Encryption: Only the browser itself can access cached data, preventing unauthorized applications or malware from extracting sensitive information.
These protections secure data at rest across both corporate-managed devices and BYOD endpoints, reducing exposure risks while maintaining productivity.
Before enforcing encryption and app-bound protections, IT teams need to understand where risks exist. The Chrome Readiness Tool, through its Browser Insights feature, provides actionable visibility:
Browser and Extension Details: Shows browser type, version, and all installed extensions across devices.
Security Threats: Highlights unverified or outdated extensions and detects devices with Session Theft Vulnerability.
Access to Unsecured Domains: Identifies visits to non-HTTPS websites or domains flagged by organizational security policies.
Once collected, the Browser Security Insights dashboard shows the security status of every device. Devices are marked as Secure only if they have zero unverified extensions and no visits to restricted domains. Administrators can drill down to view device-level data, including installed extensions, accessed URLs, and session theft vulnerability.
This insight allows IT teams to understand which devices may be handling sensitive data locally and prioritize protective measures, rather than guessing where risks lie.
Without cache encryption and visibility:
Lost or stolen devices could expose sensitive payroll or contract data.
Malware could exploit cached information to steal session tokens or credentials.
IT teams would lack clarity on which devices are high-risk.
This approach reduces the likelihood of sensitive data exposure while enabling organizations to maintain compliance and secure employee workflows.
Browser caches are an often-overlooked vector for sensitive data exposure. With Chrome Enterprise Premium encrypting local browser data and Chrome Readiness Tool’s Browser Insights providing detailed visibility, IT teams can identify high-risk devices, enforce encryption policies, and safeguard data at rest across the organization.
Start protecting local browser data today. Use Browser Insights to uncover exposure risks and CEP to enforce strong encryption and app-bound protections.

Browsers are where employees access most enterprise applications, including sensitive systems like HR portals, finance tools, and internal dashboards. While identity verification confirms who a user is, it does not inherently secure the session. Without device-bound controls, attackers can hijack sessions and bypass MFA, gaining access to critical resources.
Chrome Enterprise Premium (CEP) introduces Device-Bound Session Credentials (DBSC), binding session cookies to a specific device. Even if session cookies are stolen, they cannot be used outside the original device, ensuring corporate accounts and sensitive data remain secure.
Before applying session protection policies, IT teams must know which devices are currently exposed. Blind enforcement can disrupt users, while gaps leave your organization vulnerable.
Key questions administrators should ask:
Which devices have DBSC enabled?
Where are unprotected sessions concentrated?
Which applications rely on sessions vulnerable to hijacking?
The CEP Accelerator, part of the Chrome Readiness Tool, goes beyond basic reporting. It turns raw fleet data into actionable insights by showing where session risks exist and which CEP features can address them.
Device-Level Session Signals: Shows which devices are protected with DBSC and which are not.
Policy-Based Exposure Insights: Indicates potential session vulnerabilities.
In other words, the CEP Accelerator doesn’t just tell you “there is risk.” It answers: “Here’s which devices are exposed, and here’s what CEP can do to fix it.” This helps IT prioritize enforcement and plan a strategic rollout.
By combining visibility from the Chrome Readiness Tool’s CEP Accelerator with Chrome Enterprise Premium, organizations can:
Identify devices and sessions at risk of hijacking.
Map exposures to the appropriate CEP feature (DBSC).
Apply policy-based session protections efficiently.
Monitor coverage continuously to maintain a secure browser environment.
This structured process turns session management from reactive troubleshooting into proactive, measurable governance.
Identity verification and session security are complementary. Chrome Enterprise Premium secures the session, while the CEP Accelerator shows which parts of your environment are exposed and how CEP can fix them.
Key takeaways for IT teams:
Measure session exposure across all devices before enforcement.
Understand which CEP features address specific gaps in your environment.
Prioritize protections for devices and applications with the highest exposure.
Maintain continuous monitoring to keep session integrity intact across the enterprise.
By linking identity verification with device-bound session enforcement and visibility from CEP Accelerator, organizations ensure that sensitive data, accounts, and workflows remain protected even in hybrid and BYOD environments.
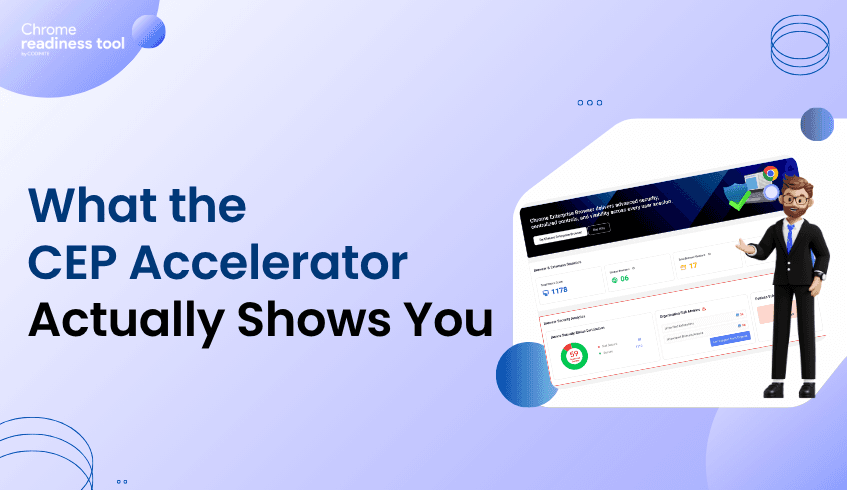
Chrome Enterprise Premium covers a lot of ground. DLP, phishing protection, context-aware access, URL filtering, extension management, security reporting. For IT teams evaluating CEP, the features aren't hard to find. What's harder is knowing which ones matter most for your specific environment right now.
That's the gap the CEP Accelerator is designed to close.
Not a Feature List. A Visibility Layer.
The CEP Accelerator isn't a tour of what CEP can do in general. It's a targeted view of where your environment has the highest exposure and how CEP's premium capabilities map directly to those gaps.
It lives inside the Chrome Readiness Tool and works from the same environment data the Chrome Readiness Tool analyzes. The difference is what it does with that data.
Instead of stopping at "here are your risks," the CEP Accelerator goes one step further: here are the risks, and here's the specific CEP capability that addresses each one.
What It Surfaces
The CEP Accelerator focuses on the areas where the jump from Chrome Enterprise to Chrome Enterprise Premium has the most practical impact.
Extension risk is one of the clearest examples. The Chrome Readiness Tool identifies unverified or high-risk extensions across your fleet. The CEP Accelerator connects that finding to CEP's extension auditing and enforcement capabilities, showing you what controlled extension management would look like in your environment specifically, not just in theory.
Session theft protection is another. The Chrome Readiness Tool shows whether each device is protected against session theft based on whether DBSC policy is active through Chrome Enterprise Premium. If CEP isn't active on a device, that device shows up as unprotected. It's a direct, device-level signal. The CEP Accelerator takes that visibility and maps it to the CEP activation that would change that status, so you can see exactly how much of your fleet is exposed and what it takes to close it.
The same logic applies to data protection gaps and phishing exposure. The Accelerator takes each risk category and ties it to the CEP feature that resolves it.
Why This Matters for IT Teams
The most common friction point in a CEP evaluation isn't budget or buy-in. It's clarity. IT teams need to be able to answer: which features do we actually need, and what will they fix?
The CEP Accelerator answers that question with your own data rather than a generic product overview. That's a fundamentally different kind of conversation to have with a decision-maker.
Instead of saying "CEP protects against session theft," you can say "here's how many devices in our fleet currently show as unprotected because DBSC policy isn't active, and here's what enabling CEP changes." That level of specificity is what moves projects forward.
What It Doesn't Do
It's worth being clear about scope. The CEP Accelerator is a visibility and planning tool. Session theft protection status, for example, reflects whether DBSC policy is active through CEP, it's a policy coverage indicator, not a real-time attack monitor. What the tool gives you is an accurate picture of where your devices stand today and which CEP capabilities would change that.
The value isn't in alerting. It's in connecting your actual environment to the right premium capabilities before you deploy, so you're not guessing at configuration priorities after the fact.
CEP Accelerator: Now Available in Chrome Readiness Tool
The CEP Accelerator is now live inside the Chrome Readiness Tool. Run an assessment, open the Accelerator, and you'll see your environment mapped against CEP's premium features in a way that makes deployment decisions significantly easier to justify and act on.

Most IT teams don't lack interest in Chrome Enterprise Premium. They lack visibility. They know threats are increasing, they've heard the pitch, and they can see the value on paper. But when it comes time to justify the investment or even know where to start, the answer is usually the same: "We need more data first."
That's exactly the problem the Chrome Readiness Tool was built to solve.
The Readiness Question Nobody Can Answer Off the Top of Their Head
Ask an IT admin whether their org is ready for CEP and they'll probably hesitate. Not because they don't understand what CEP does, but because readiness depends on knowing your current environment, and most teams don't have that picture clearly laid out.
Are there high-risk extensions running across your fleet? Are unverified extensions slipping through? Are there active session risks that policies haven't addressed yet? Are your existing Chrome policies actually doing what you think they're doing?
Without answers to these questions, any readiness conversation is just guesswork.
What Chrome Readiness Tool Actually Does
Chrome Readiness Tool works with data from your managed browser environment, giving you a structured readiness report across multiple risk categories including extension risk, session integrity signals, and policy coverage.
You're not filling out a checklist. You're looking at your actual fleet.
The tool surfaces things like: which extensions across your environment are unverified or flagged as high risk, where session-related risks exist based on configured policies, and how your current browser setup compares against CEP-relevant security benchmarks.
For most teams, the first Chrome Readiness Tool scan is a bit of a wake-up call. Not because things are catastrophically broken, but because the gaps are specific and visible in a way they weren't before.
Readiness Isn't Binary
One thing Chrome Readiness Tool makes clear is that readiness isn't a yes or no. It's a spectrum. Some parts of your environment might already align well with what CEP requires. Others might need attention before you get full value from a premium deployment.
That's actually useful information. It lets you prioritize. If extension risk is your biggest gap, you know where to focus first. If your session integrity signals are mostly covered by existing policies, that's one less thing to build a case around.
Chrome Readiness Tool turns a vague readiness question into a specific, actionable gap analysis.
Using Chrome Readiness Tool to Plan Your CEP Rollout
Once you have your Chrome Readiness Tool report in hand, the path to CEP becomes a lot more structured. You know which areas need the most attention. You know which CEP features will address the highest-concentration risks. And you have the data to walk leadership through the why before committing the budget.
This is the entry point most IT teams need: not a sales pitch, but a mirror. Chrome Readiness Tool shows you your own environment and lets you decide what the next step looks like.
The CEP Accelerator: Connecting the Dots
The CEP Accelerator feature within Chrome Readiness Tool takes this a step further. Instead of leaving you to manually connect readiness findings to specific CEP capabilities, it does that mapping for you. It highlights which parts of your environment would benefit most from CEP's premium features, from DLP and phishing protection to context-aware access and extension management.
This feature is coming soon and will give IT teams a faster path from readiness assessment to deployment planning.
Start With What You Know
If you've been putting off the CEP conversation because you didn't know where to begin, Chrome Readiness Tool is the beginning. It takes your existing Chrome environment, surfaces the risk data that matters, and gives you a clear picture of where you stand.
Readiness isn't something you declare. It's something you measure. Chrome Readiness Tool makes that measurement straightforward.